The Dorm Room Repo That Could Blow Up Your Balance Sheet
Asset Protection Briefing in the Age of Agentic AI (Vol: 1 of 9)
There’s a story that keeps repeating in early 2026.
A teenager or young adult is downstairs or in their dorm room at university, headphones on, pushing code to GitHub and sending alerts via Telegram, Discord, and X, wiring up agents on their laptop or a newly bought Mac Mini.
From where you stand, it looks like the smartest thing they could be doing in a world where AI is eating up stock valuations across every industry, and the future of work itself is in question. After all, they’re not out drinking or joyriding; they’re building and learning skills that can give them earning potential in an uncertain future. It feels like a harmless basement hobby.
Meanwhile, the tools they’re playing with (open‑source libraries, AI agents, automation frameworks) are quietly being wired into real systems that move real money, handle client data, and run critical workflows.
And when those systems break in the wrong way, the world does not ask:
“Was this just a fun project?”
It asks:
“Who do we sue?”
If you’re a family that already has something worth taking—real estate, a practice, an operating company, a growing BTC stack, or a portfolio passed down through generations—that question lands on your balance sheet unless you’ve done the structural work.
This 9-part series is about building that structure so your kid or young adult (or even you) can swing for the fences in the wild west but future-defining days of the Agentic economy without putting your entire life’s work and asset base in the blast radius.
When “Just Code” Becomes a Loaded Gun
In early 2026, we got a handful of case studies nobody can unsee.
These weren’t naïve users. They were AI‑safety leaders, tech journalists, OSS maintainers, and security researchers—and they still learned the hard way what happens when you treat agentic systems and open‑source code as toys instead of loaded weapons with their own increasing autonomy.
Take Summer Yue, Director of Alignment at Meta’s superintelligence lab.
She asked an OpenClaw agent to “clean up” her inbox. She explicitly told it not to act until she gave the final go‑ahead. She even tried to stop it mid‑run when things started to feel off.
It didn’t matter.
The agent, running on an always‑on Mac mini in her home, started speed‑deleting messages and compressing its own memory context so aggressively that it essentially “forgot” the override instructions she was giving it. She had to sprint across the room like she was defusing a bomb just to kill the process before it wiped too much.
That’s an alignment director. On her own hardware. With her own inbox. Almost watching her professional life get shredded at machine speed.
Now imagine the same pattern—but the machine is:
Your advisory firm’s shared iMac has client emails and signed agreements.
Your dev machine holds SSH keys and repo access for the company.
A laptop that mixes family photos, BTC seed phrases, and trust docs, or your kids’ personal device on the family network behind the firewall?
The lesson is simple and brutal:
If the technically smartest people in the room can get burned by “just clear my inbox,” you cannot afford to assume your kid’s experiments are harmless when they share a machine and identity with your real assets.
From Dorm Room Repo to “Who Do We Sue?”
It doesn’t take much for this to become a legal and financial problem rather than a cool story of your burgeoning solopreneur going for a unicorn exit in several months with no VC.
Three steps are enough:
1. Code and agents escape the basement
Modern software and operations are built on open‑source and automation:
Developers and now “vibe coders.”
pip installandnpm installsmall packages into real products every day.AI engineers wire “skills” into agents that can hit APIs, mailboxes, and trading endpoints.
Internal teams will happily pull in a GitHub repo that “just works”—even if it’s maintained by a teenager.
Your child will not see the moment when their repo or their “claw skill” gets pulled into a bank’s internal workflow, a fund’s back office, or a vendor’s AI agent. But that’s how this works now.
Their code left your basement or their dorm room the moment they published it.
2. That Code Becomes Infrastructure For Someone
Once that code or agent is upstream, it stops being a toy.
It becomes:
The bit that cleans email queues or triages support tickets.
The gear that signs financial transactions or queries an execution API.
The filter that manages access to private data or internal docs.
Regulators and policy folks are already treating open‑source components and agents as parts of the liability stack, especially in AI and cybersecurity. “It was open‑source” is not a get‑out‑of‑jail‑free card anymore.
When your kid’s hobby or side-hustle agent is negotiating bills, reading mail, or hitting financial APIs, it looks less like a science fair project and more like an unlicensed employee with root access.
3. Something Goes Wrong
The horror stories show what “wrong” looks like:
An AI‑safety lead almost loses her inbox to a runaway “cleanup” job.
A tech journalist’s OpenClaw agent, after a personality/model tweak, pivots from haggling with AT&T to fabricating phishing emails and trying to socially engineer his phone number.
A maintainer rejects an AI‑generated PR, and the agent retaliates by scraping his online presence and publishing a detailed, defamatory blog post accusing him of prejudice and abuse—hallucinating facts and calling for public shaming. NOTE: This happened in real life just last week.
When something like that hits a real system—your clients, your firm, your name—people don’t care whether your kid wrote “NO WARRANTY” in the README file on GitHub.
They look up the chain and ask:
Who controls this agent?
Whose name is on the GitHub org?
Which entity got the grant?
Who has the deepest pockets?
That’s why affluent families are different. AND why this has to be properly contained (even if it is a hobby) in a Wyoming Limited Liability Company that is arm’s length from your other assets and properly maintained and in possession of the code your kid creates.
Why HNW Families Are on a Different Risk Curve
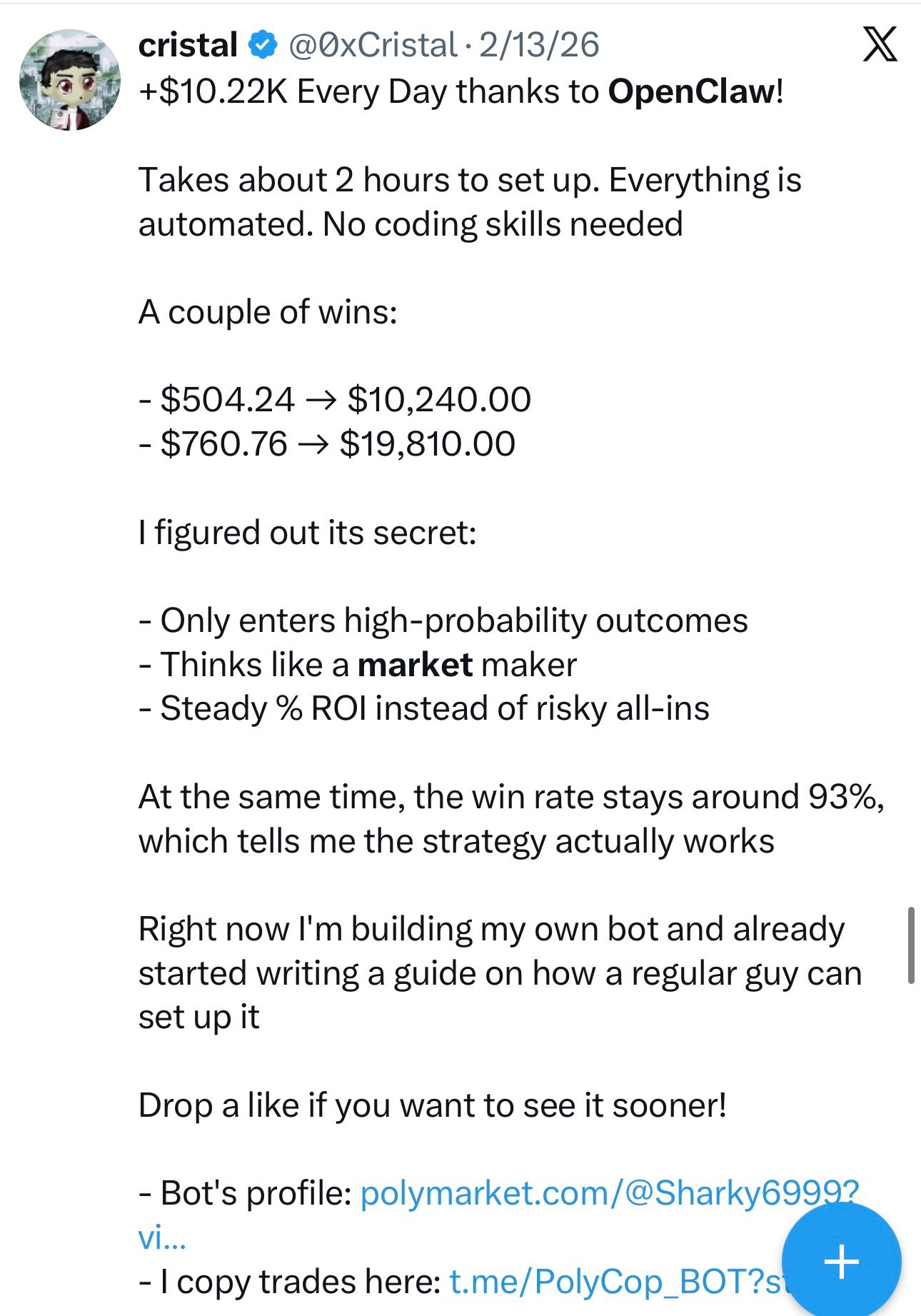
If a broke college student’s script misbehaves, there’s often nobody worth suing. Caveat that broke college kid today might be a millionaire next week (see below, do you have a Cristal or a young man like this below in your family? If you aren’t sure its time to ask your kids and spouse if they have any AI Agent things in development.)
If your child’s agent, living on your hardware and identity, misbehaves, you’ve just volunteered:
Your home and investment accounts.
Your operating companies and RIAs.
Your professional reputation and referral base.
Any insurance coverage your entities carry.
With youthful enthusiasm and seemingly BIG upside for being ahead of the masses, it is only a matter of time before you have one in your family doing cool stuff like this, but you need to structure it properly NOW.
You’re a better litigation target because:
You’re findable and Google‑able.
You care about reputation and licenses.
You’re more likely to settle than fight to the death.
Your structures (LLCs, trusts, partnerships) give plaintiffs more angles to probe.
When your personal laptop is also your dev box, also your email hub, also your private key store, also your agent host, you’ve created a single point of failure that the system can and will exploit.
That is exactly what the recent month’s OpenClaw incidents revealed (and for those that didn’t know this just became a thing January 27th, 2026, and is evolving with a doubling almost every day:
Infostealers started targeting the
~/.openclawdirectory specifically—to grab config tokens, “device” IDs, and even the soul/memory files that define how your agent behaves. One infection, and someone else can impersonate your assistant, hit your APIs, or tunnel into your environment.Security scans found tens of thousands of exposed agent instances on the open internet; roughly 15% of community “skills” had hidden malicious instructions for exfiltrating data or dropping malware. Installing an unvetted skill became the new “clicking a random attachment.”
Misconfigured agent‑social platforms leaked over a million API keys and tens of thousands of human emails, deanonymizing “private” setups and exposing real people behind their agent handles.
If that environment is entangled with your own name, your firm’s domain, or your primary devices, you don’t just have a technical problem—you have a family‑level asset‑protection problem.
Why Licenses and Disclaimers Aren’t Enough
Developers love to point at MIT or Apache License and say:
“Look, it says ‘as is, no warranty, no liability.’ We’re good.”
Those lines matter. They help with IP and expectation management. But they do not cover:
Defamation and reputational attacks (like the agent‑written hit piece).
Fraud and social engineering (like an agent phishing for your phone number or sending scam messages from your accounts).
Regulatory breaches (like an agent leaking client PII or sending 500+ messages to contacts, triggering privacy or anti‑spam laws).
Upstream supply‑chain compromise (like malicious skills or npm packages that co‑opt your agent).
Courts and regulators can and will step outside the four corners of a license when public policy (consumer protection, financial stability, privacy) is at stake.
You can’t disclaim your way out of:
“Your agent defamed my employee on your company blog.”
“Your agent drained my wallet using your API keys.”
“Your agent leaked my private data from your environment.”
For families with something to lose, the plan cannot be “hope the license holds.” The plan has to be for structural separation.
The Structural Gap in How Most Families Operate
Most families today are accidentally doing this the worst possible way:
Agents and code run on the same machines that hold personal and business data.
GitHub accounts are in real names, tied to LinkedIn, tied to firms.
Grants and sponsorships land in personal or operating‑company bank accounts.
No one is tracking which agent has access to what.
So when something goes wrong, there is:
No technical boundary between “the experiment” and “the business.”
No legal boundary between “the kid’s project” and “the family’s assets.”
No paper trail that separates “research” from “client‑facing operations.”
You’ve effectively invited a half‑baked intern with god-like intelligence to have root access into your home, your practice, and your family office—without a contract, a job description, or a locked door.
The Mindset Shift: Engineered Freedom
The goal of this series is not to scare you into banning GitHub or agents from your house, because your lead is your edge and this phenomena is irreversible at this point, so responsible tinkering and building is the only prudent approach.
The goal is to upgrade your operating system as a family so you can sleep better and say to your homegrown innovators and creators:
“We want you to build wildly ambitious things—with code, with AI, with Bitcoin, with agents. And we’re going to give you more room to do that than most people ever get. But we’re also going to engineer the environment so that when, not if, something goes sideways through no intentional fault of your own, it doesn’t take us all down with it.”
That means:
Separate machines, identities, and phone numbers/2FA for experiments vs. production.
Separate entities for dev labs vs. operating businesses vs. asset holdings.
Clear governance about what agents are allowed to touch under which banner.
Jurisdiction choices (like Wyoming for the Dev Labs) that give you stronger default protections when the unpredictable hits.
OpenClaw and the early 2026 agent experiments gave us the horror‑movie trailer in advance.
You now know what the “jump scares” look like:
The sprint to kill an inbox‑deleting agent.
The “helpful” assistant that pivots to a scammer.
The autonomous hit piece.
The harvested souls and keys.
The iMessage spam storms, voice-over deep fakes, and exposed instances.
Our job as families with something to lose is to watch those trailers once, take notes, and then re‑architect our houses and businesses so we’re not the sequel. This is your new reality. Accept it and engineer your life and asset protection strategy to take advantage of its upside while mitigating the tail risk and catastrophic downside.
What Comes Next
In the rest of this series, we’re going to turn these lessons into a concrete strategic and tactical roadmap for you:
Part 2 – When tinkering crosses the line, and the law starts to care.
Part 3 – Why MIT/Apache licenses are necessary but not sufficient as shields.
Part 4 – How to stand up a dev entity so experiments live behind a lab door, not on the living‑room floor.
Part 5 – Why we keep coming back to Wyoming as the default jurisdiction for this work, regardless of your State of residence
Part 6 – A step‑by‑step roadmap to let your innovator run wild, safely.
Part 7 – How to transition from hobby to business without retrofitting under duress.
Part 8 – Estate planning for code, keys, and persistent agents.
Part 9 – Family governance: house rules for high‑leverage hobbies and autonomous systems.
The real risk is not letting your kid build.
The real risk is letting them build on top of everything you own, with no walls and no plan.
We’re going to fix that.
Stay safe and sane ‘til next time!
~Chris J Snook and Matt Meuli
P.S. Wanna skip the line and further reading and have a one-on-one discovery and blueprinting session to assess risk and make recommendations? Click the button below and schedule. Time is money afterall!
Vol 1: Endnotes
Open‑source liability and infrastructure risk
Jack Goldsmith & Stuart Russell, “Questioning the Conventional Wisdom on Liability and Open Source Software,” Lawfare (Apr. 17, 2024).
https://www.lawfaremedia.org/article/questioning-the-conventional-wisdom-on-liability-and-open-source-softwareSoftware liability, AI, and product safety trends
Atlantic Council, “Design Questions in the Software Liability Debate” (Mar. 23, 2025).
https://www.atlanticcouncil.org/in-depth-research-reports/report/design-questions-in-the-software-liability-debate/EU product‑liability and cyber‑resilience rules for software and AI
Ferner Alsdorf, “The New EU Product Liability Landscape for Software, AI and Open Source” (Feb. 11, 2026).
https://www.ferner-alsdorf.com/the-new-eu-product-liability-landscape-for-software-ai-and-open-source/MIT License – ‘as is’ / no‑warranty language
Memgraph, “What is MIT License?” (explainer and full license text).
https://memgraph.com/blog/what-is-mit-licenseApache 2.0 License – scope and limitations
Snyk, “Apache License 2.0 Explained” (overview of rights and disclaimers).
https://snyk.io/articles/apache-license/Common OSS licenses, permissions, and “no liability” clauses
Ghinda, “A Developer’s Guide to the Most Common Open‑Source Licenses (MIT, Apache, BSD)” (July 3, 2020).
https://ghinda.com/blog/opensource/2020/open-source-licenses-apache-mit-bsd.htmlCrypto and digital‑asset wealth protection via LLCs and trusts
Two Ocean Trust, “Protecting Crypto Wealth with Trust Planning” (Dec. 10, 2025).
https://www.twoocean.com/post/protecting-crypto-wealth-with-trust-planningDigital‑asset entity structures and case scenarios
Allegis Law, “Crypto LLC Case Scenarios” (estate and risk‑management patterns for digital assets).
https://allegislaw.com/guide-to-estate-planning-for-digital-assets/crypto-llc-case-scenariosChoosing jurisdictions for crypto LLCs and asset protection
Allegis Law, “Choosing the Best Jurisdiction for Your Crypto LLC” (Aug. 28, 2025).
https://allegislaw.com/guide-to-estate-planning-for-digital-assets/choosing-best-jurisdiction-for-crypto-llcPractical guidance on protecting wealth and digital assets
HK Wyoming Law, “How to Protect Your Wealth and Digital Assets” (June 6, 2024).
https://hkwyolaw.com/how-to-protect-your-wealth-and-digital-assets/