Why High Net Worth Families Need to Implement a Family-Agent Constitution ASAP!
Asset Protection Briefing in the Age of Agentic AI (Vol: 8 of 9)
There comes a point when the question is no longer whether one promising AI project needs a structure around it. The real question becomes what happens when there are several of them—spread across siblings, family branches, trusts, operating companies, and the family office itself.
That is the threshold this volume is about.
The process of distilling compounding complexity now into a simple (yet complete) family-agent constitution is the best investment you can make this year, as it will only become more difficult, important, and cumbersome in future years to get started.
If Volume 7 was the chapter about deciding what to do when one vibe-coded project becomes commercially real, Volume 8 is where the aperture widens.
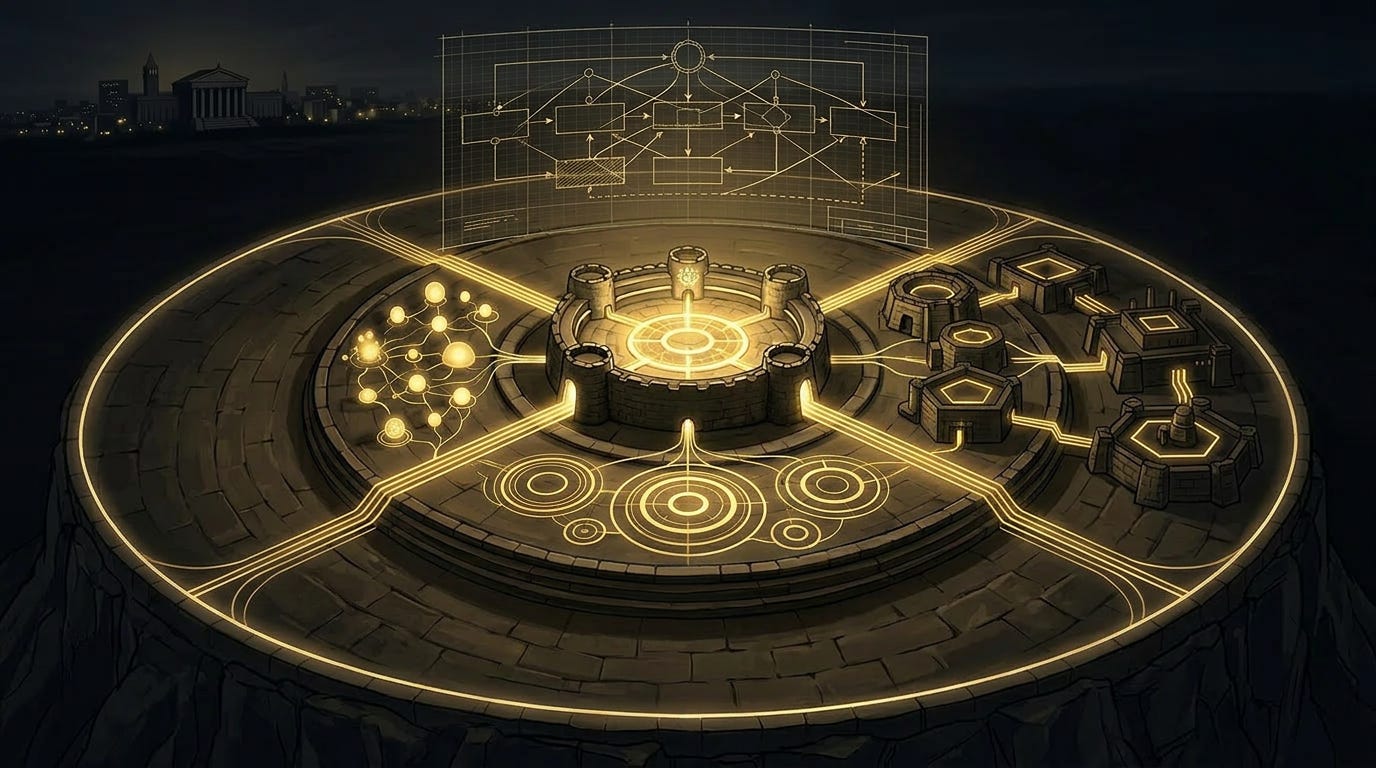
This segment is where you stop looking at a single builder, a single LLC, or a single agent in isolation and start seeing the family as a living system of systems. One child is building workflow agents. Another branch is experimenting with research copilots or investment intelligence. An operating company is quietly embedding AI into compliance, sales, or operations. A family office wants the leverage, but not the exposure. A trustee wants to know what exactly is being owned, delegated, and passed on.
That is when you need more than enthusiasm, more than one good lawyer, and more than a clean Dev Lab/Ops split. You need a shared, single-page constitution.
Not a novelty document. Not a manifesto. Not a consultant’s binder full of language nobody will ever use. A real constitution: short enough to govern with, clear enough to survive pressure, and durable enough to outlast whichever family member happens to be the technical genius in the room this year.
The reason this becomes necessary faster than most families think is simple: agentic systems do not arrive one at a time. They arrive sideways. One begins as a kid’s side project. Another slips in through a vendor tool. A third gets adopted by a hungry operating executive who wants speed. A fourth gets built inside the family office because someone is tired of repetitive admin work.
Before long, the family no longer has “an AI project.” It has an ecosystem of automations, decision layers, data flows, and delegated actions, all developing under different incentives and with different assumptions about what is allowed.
That is the moment local governance stops being enough.
The second multiple systems begin touching shared assets, shared data, shared reputational surfaces, or shared counterparties, they are no longer separate technical curiosities. They are now a family governance issue. The family that says, “We trust the kids, we trust management, and we trust the advisors,” but never defines common boundaries, is not being adaptive. It is simply postponing conflict until the stakes are much higher.
So the purpose of a family agent constitution is not to make the family feel bureaucratic. It is to create a common operating philosophy before complexity chooses one for you. It answers the questions that otherwise get answered informally, emotionally, or too late: what counts as an agentic system in this family, where those systems are allowed to live, what they are allowed to touch, who has the authority to approve them, and who is responsible when they fail.
At the highest level, every serious family constitution needs to answer four core questions.
First, what counts as an agentic system? If a system can perceive inputs, make decisions based on logic or model output, and take action with real-world consequences, it belongs in scope. That includes copilots with privileged access, workflow automations that move data or trigger financial consequences, research systems that influence investment decisions, communications systems that speak externally, and vendor tools with embedded delegated authority.
Second, where those systems are allowed to live. Some belong only in the Dev Lab. Some can exist in internal-only environments. Some may be approved for production use through Ops or a designated operating company. And some should never be permitted anywhere near family systems at all. Earlier volumes gave you the containers. Volume 8 turns those containers into family law.
Third, what those systems are allowed to touch. Can an experimental agent access trust records? Can a next-generation builder use shared family APIs for a side project? Can an operating company’s internal AI reach the family office document base? Can any model train on family correspondence, legal documents, or sensitive identity records? This is the heart of the constitution, because “can it” and “should it” are rarely the same thing.
Fourth, who is actually responsible? Not just who wrote it, but who owns it. Who approves deployment? Who reviews incidents? Who can shut it down? Who authorizes exceptions? Who steps in if the builder disappears, burns out, gets acquired, moves overseas, or simply loses interest?
If the family cannot answer those four questions across its meaningful systems, then what it has is not governance. It is a pile of projects waiting to intersect.
One of the most useful moves a family can make at this stage is to build a map of the different classes of systems already forming around it. In practice, most families will find three categories emerging.
The first are sibling systems. These are next-generation builds—projects created by individual children or younger family members, often at very different levels of seriousness. One may be building a genuinely investable product. Another may just be experimenting, but experimenting with real infrastructure and real risk. A third may be brilliant but operationally careless, which is often more dangerous than obvious recklessness. These systems need room to develop, but they cannot be treated as private hobbies once they begin touching common assets or shared family surfaces.
The second are branch systems. These belong to particular branches of the family, trust structures, or sub-enterprises. They may feel independent because they have their own capital, their own advisors, and their own local decision-makers. But they still often ride on shared reputation, shared family relationships, or shared infrastructure. The constitution has to respect branch autonomy without pretending branch actions are totally sealed off from the rest of the family.
The third is operating company systems. These are the most economically consequential and often the most operationally dangerous.
They live inside real businesses. They touch employees, customers, vendors, counterparties, and compliance obligations. They are usually built under pressure, because operating teams want speed and leverage now, not after a year of policy work.
That is precisely why they need constitutional clarity.
The purpose of the family map is not to erase these distinctions. It is to allow all three categories to exist while still plugging into a common governance layer. That is what prevents creativity from turning into federated chaos.
To make that governance usable, the constitution needs a simple classification system. If the system is too complicated, nobody will use it. If it is too vague, it will be ignored. A four-tier model is usually enough.
From Bottom to the top:
Tier 1 is Experimental. These systems live in the lab. They use synthetic, low-risk, or tightly controlled data. They do not touch production systems, shared family identity, regulated workflows, or meaningful money movement. They are allowed to fail.
Tier 2 is Internal Assisted. These systems can support people internally but cannot independently bind, message, move, approve, or execute in high-risk ways. They may see more sensitive data, but only inside approved environments and with clear boundaries.
Tier 3 is Operational. These systems sit inside live workflows. They affect customers, employees, investment processes, counterparties, or economically material decisions. They must be logged, reviewable, tied to a responsible entity, and visible to someone beyond the original builder.
Tier 4 is Controlled Autonomous. These systems are permitted to take significant action with limited or conditional human review. This category should be rare. It requires explicit approval, tested kill switches, clear escalation paths, and recurring review at a level above the local operator.
This kind of classification does something deceptively important: it gives the family a shared language. A drafting assistant is not a customer-facing negotiator. A summarization bot is not a trading layer. A research copilot is not a trust-admin system with permission to route sensitive documents. Families need a way to distinguish these systems without collapsing into technical jargon or emotional argument every time a new tool appears.
That shared language becomes even more important when you define the constitution’s non-negotiables. Every serious family should have a short list of actions or permissions that cannot be delegated casually to machines. The exact list will vary, but the principle should not.
No system should be able to move meaningful money, trigger capital calls, or authorize transfers without defined approval thresholds and review logic. No system should be permitted to send external messages in the voice of the family, the family office, trustees, or key entities without explicit authorization and logging. No agent should have unrestricted access to estate plans, trust documents, health records, identity records, or family governance materials. No model should be allowed to train on highly sensitive family data just because the data is “available.” And no important system should depend entirely on one person’s laptop, memory, or private credentials.
These are not anti-innovation rules. They are the price of adulthood.
One of the most useful things the constitution can do is force clarity around containers. Every meaningful agentic system needs a home. Not metaphorically. Legally and operationally. Some systems belong in Dev Lab entities. Some belong in Ops. Some belong inside a family office environment. Some belong in operating companies. Some may sit in trust-owned holding structures or specialized wrappers tied to digital-asset governance. What matters is that every serious system has a defined container and a reason it lives there.
That single discipline prevents a tremendous amount of sloppiness. It stops “temporary” projects from quietly becoming permanent infrastructure without ever being assigned to the right entity or risk box. It also makes succession, diligence, incident response, and eventual exits much easier because the family is no longer trying to reconstruct architecture from memory.
The same is true for identity and access. Families tend to think in terms of entities and legal documents, but many of the biggest failures happen lower in the stack.
Who has the admin credentials?
Which systems share tokens?
Which family member has hidden superuser access in six places?
Whether production systems are still tied to personal emails or business entity/family office accounts.
Whether a burned-out builder can accidentally—or intentionally—take a meaningful system dark because nobody else has the keys.
A real constitution should set family-wide principles for identity and access, even if the detailed procedures live elsewhere. Shared family credentials should not be used for personal experiments. Production systems should use entity-owned accounts, not student emails and improvised admin paths. Role-based access should exist for systems touching sensitive or economically material data. And every important production system should have a recovery path that does not depend on the goodwill or memory of the original builder.
If that feels boring, good. Boring is what healthy governance feels like when it is working.
Now, because none of this sustains itself, most serious families will eventually need some version of a family agent council. Not a bloated committee. Not another ceremonial board that meets twice a year and understands none of the underlying systems. A small, recurring governance body with just enough technical, legal, operational, and family context to preserve constitutional integrity across the ecosystem.
Its role is not to micromanage every experiment. Its role is to make sure the experiments, internal systems, and operating deployments remain legible inside one family-wide framework. In practical terms, that means approving Tier 3 and Tier 4 deployments, reviewing exceptions, tracking incidents, maintaining system inventories, clarifying which agents live in which containers, and making sure no mission-critical system is one resignation or one family conflict away from becoming ungovernable.
The need for this council becomes acute the moment one family-controlled system starts interacting with another. This is the transition point most families underestimate. A research agent in one operating company begins feeding an investment workflow. A family office assistant starts pulling from portfolio company data. A sibling’s planning tool gets connected to the family CRM because “it’s easier.” A branch-specific system leans on centralized identity infrastructure because no one wants to duplicate setup work.
Each connection feels small. But once multiple systems start interacting, the real risk is no longer just what each one does in isolation. It is what no one can clearly see across the combined network. Permissions become transitive. Sensitive data moves across invisible seams. Accountability blurs. Failures propagate.
That is why the default rule should be simple: no cross-system connection by default. If one agentic system is going to rely on, pull from, or trigger another, there should be a short written interoperability memo. It does not need to be ornate. It just needs to answer:
What is connecting to what?
What data is crossing the boundary?
What actions can follow from that connection?
Who benefits?
What can go wrong, and who shuts it down if the connection creates risk?
That one-page habit alone can save families years of future confusion.
This is also where succession stops being a legal abstraction and becomes an operational one. If the family succeeds in building multiple intelligent systems, then heirs are not merely inheriting LLC interests, trust distributions, or operating cash flows. They are inheriting logic, delegation, permissions, and invisible infrastructure. That is a very different kind of estate.
Which means a real succession plan cannot stop at who gets the equity. It also has to explain what exists, why it exists, how it fits together, which parts are mission-critical, which parts should be audited, wound down, or separated, and who has interpretive authority if the constitution itself becomes a source of dispute. In practical terms, that means the constitution should be paired with a plain-English succession appendix—something an intelligent heir, trustee, or future operator can actually read ten years from now without needing to reverse-engineer the family’s entire technical history.
That translation function may be one of the highest-value things a founder-builder can ever do for a family. Not just building the thing, but making the thing survivable.
So what does a workable constitution actually look like? Usually something much shorter than people expect. Ten to fifteen pages is enough for the constitution itself if the inventories, diagrams, and procedures live in appendices or operating manuals. A useful structure would cover purpose and scope, definitions and classification tiers, approved containers, data and permission rules, approval pathways, oversight and escalation, incident response and shutdown authority, continuity requirements, interoperability rules, and amendment procedures.
That is enough. More than that, you are often writing a museum piece rather than a governing document.
For families ready to operationalize this, the path can be surprisingly manageable. In the first week, build a complete inventory of every meaningful AI, automation, or agentic system across the family office, operating companies, branches, next-generation projects, and meaningful vendor systems. In the second week, classify and containerize each one—Experimental, Internal Assisted, Operational, or Controlled Autonomous—and assign it to its current and intended legal home.
In the third week, draft the constitutional non-negotiables: the one-page list of what the family will not delegate casually, how sensitive data is handled, what counts as prohibited production shortcuts, and where single-person dependency is unacceptable. In the fourth week, establish the oversight body, define what requires review and what does not, assign ownership of the inventory, and schedule the first actual meeting. Then, over the next two weeks, write the succession appendix in human language: what exists, why it matters, which systems are foundational, which risks are known and accepted, and how a future heir or trustee should approach the ecosystem.
If you do Volume 8 well, several things happen at once.
Builders gain more freedom, not less, because they know which zones are safe for experimentation and which require elevation.
Trustees and advisors become useful instead of reactive because they have a framework for asking good questions.
Family branches keep more autonomy without pretending interdependence does not exist.
And succession becomes more legible because the family is no longer inheriting black boxes; it is inheriting a governed architecture.
That is the real promise here.
The family-agent constitution is not about controlling the future. It is about making the future governable.
The families that thrive in this next era will not necessarily be the ones with the smartest models or the earliest experiments. They will be the ones who learn how to turn intelligence into structure without crushing what made it valuable in the first place.
~Chris J Snook and Matt Meuli
P.S. If you are interested in eating this proverbial “elephant” one small bite at a time, while we customize and hold your family’s hand through each nuance of design and deployment, then don’t hesitate and book your one-on-one blueprinting consult today.
Vol 8 Sources:
NIST, “Artificial Intelligence Risk Management Framework: Generative Artificial Intelligence Profile.” <https://www.nist.gov/publications/artificial-intelligence-risk-management-framework-generative-artificial-intelligence>nist
OECD, “AI principles.” <https://www.oecd.org/en/topics/sub-issues/ai-principles.html>
Wyoming Secretary of State / Wyoming DAO FAQ resource, “Decentralized Autonomous Organization (DAO) Frequently Asked Questions.” <https://wyomingdiscountregisteredagent.com/decentralized-autonomous-organization-dao-frequently-asked-questions>wyomingdiscountregisteredagent
Grupp Law, “The Benefits of a Wyoming Private Family Trust Company.” <https://grupplaw.com/insights/wy-private-family-trust-company/>grupplaw
Nolo, “LLC Asset Protection and Charging Orders: An Overview of State Laws.” <https://www.nolo.com/legal-encyclopedia/llc-asset-protection-charging-orders.html>nolo
Plant Moran, “Innovating with AI: A governance framework for family offices.” <https://www.plantemoran.com/explore-our-thinking/insight/2026/03/innovating-with-ai>plantemoran